5 little tricks to enhance Jira workflow with LDAP data
Every company looks for ways to improve their workflow and avoid any delays. Especially big corporations where is so many people that it’s easier to manage the most complex management tool than to remember everyone’s names. However, a great workflow without bottlenecks is often created by implementing small, but tremendously helpful tricks. Even simple automation of some administrative activities can greatly affect company’s processes. One possible way is to provide a tighter connection between Jira and the LDAP server like Active Directory.
Connecting Jira to LDAP
Active Directory uses a domain structure to contain and organise information about shared resources such as servers, volumes, printers and accounts: users, groups and computers. It stores information such as names, passwords, phone numbers, etc., and makes it searchable. Then, web applications can use LDAP, or Lightweight Directory Access Protocol, to look up this information. There are a few LDAP servers on the market, and fortunately Jira provides built-in connectors for the most popular ones, such as Microsoft Active Directory, Apache Directory Server, Fedora Directory Server and a bunch of others. There is a step-by-step guide to establishing LDAP connection on the Atlassian documentation.
We will help you make the best choice
We want to invite you to a consulting session during which we will jointly decide which ITSM One Edition is the best One for you.
Even though we can integrate Jira with Active Directory natively, the default integration doesn’t enable the synchronization of users’ attributes. Of course, we can import their accounts manually, but it’s much easier to synchronize user data automatically and thus keep them always up-to-date. Active Directory Attributes Sync is one of the apps available on Atlassian Marketplace that enable advanced use of LDAP data in Jira. With the app installed, we can display users’ attributes in a couple of places, as well as perform some actions on the LDAP server with no need to wake up the admin.
Advanced use of Active Directory data in Jira
Automated Active Directory account management
Sometimes, big companies struggle with onboarding a new employee right away on their first day at work. In most cases, it’s not caused by unprepared working space or hardware, but rather by admin-related tasks like creating new user in the database, granting permissions, and so on, because Active Directory admin needs to take care of this and not Jira admin or even a project admin. However, it’s possible for us to deal with this automatically – we can add the Update Data post function to our workflow to automate creating a user account in Active Directory when creating an onboarding task.
Moreover, we can select other options to update and manage Active Directory user data from the Jira instance. Probably all of us set various passwords for different accounts, which makes it easier to type in the wrong one when logging in at work before we have the first coffee in the morning. We can ask the Active Directory admin to reset our password, but we can also simply create a Reset Password task in Jira which will trigger the same post function configured differently. The password will be automatically stored in a custom field which we recommend to set as Secure, and when the task is In Progress, this post function will also unlock the user in Active Directory. This way, we get a new password and can log in again almost immediately.
The same goes for changing user’s attributes like Email, Job Title, Phone Number, etc., as well as removing user from the Active Directory or managing group memberships. Each of these actions can be done with a different setup of the same post function. This way, we don’t have to worry about how changes in the company will impact our work, because we’ll be able to create a Service Desk issue with specific value we need to change that will trigger automated update of the specified attribute in both Jira and Active Directory. The Update Data post function also automates removing users and adding them to groups by simply making transitions of the right Service Desk issues that will either automatically give permissions to user or take them off the list.
Employees’ information at hand
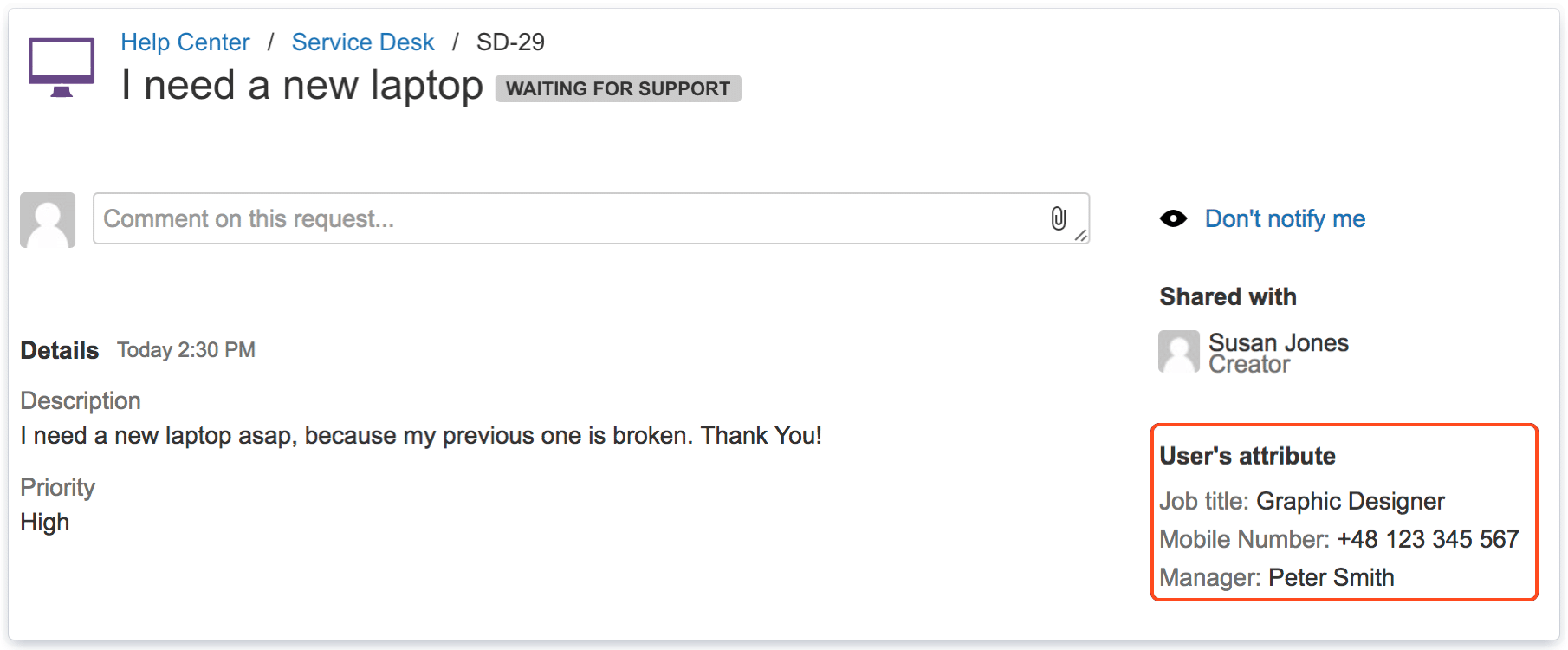
Once we synchronized Active Directory with Jira, we can display some information about our employees – not only in their public profile or hover dialogue, but also on the issue view and Customer Portal. It comes in handy when we want to provide our customers another way of communication with agents, because we can show them an agent’s email address or even phone number. The same goes for dealing with internal issues, when the employees can simply check out who’s taking care of their requests and reach out to an assignee outside company’s Service Desk.
What’s more, we can also add an agent’s supervisor to their requests by adding another post function Copy Property to the workflow. Thanks to this, a manager will be able to have an eye on what their subordinates are dealing with, and their information will also show up on Customer Portal or the issue view in dedicated custom field.
Advanced Jira approvals
We can use synchronized data not only in case of some administrative actions but also to use advanced conditions. One of them protects us from executing requests by our agents that are costly for the company. For example, if only managing staff can request for more expensive gear or 5-star hotel bookings, we can require acceptance from the top management, and no one else can push these tasks forward. We only need to set up manager’s attribute from Active Directory as the Approver, and such requests will need an approval from the higher-ups. And in case if a manager leaves the company and is replaced by a new one, this condition automatically updates the configuration.
Search for issues by Active Directory attributes
Another little trick helps us search issues for attributes synchronized from Active Directory server. Whenever we need to find a custom field, reporter or assignee, we only need to specify a JQL query by providing three arguments: custom field/reporter/assignee, an attribute, and its value. For example, when we’re looking for a developer who works in the company’s office in San Francisco, we provide such a query:
issue in searchFromAD(“Developer”,”City”,”San Francisco”)
Azure AD Attributes on Jira issue view
When using Jira Cloud and Azure Active Directory, we can obtain additional information about the users with our Azure AD Attributes for Jira application, available on Cloud. The app matches Azure and Jira users based on selected attributes and displays their contact details on issue and request views.
Our solution also includes automatically copying user properties (as manager or department) to custom fields via the post function. The application fetches data of reporters, assignees, and other users – selected in the user picker field.
Trick or treat for a workflow?
It’s not Halloween and we don’t need to ask ourselves that questions, but it still fits in this situation. Making use of the synchronized data from our Active Directory is both a trick for us and a treat for our workflow to make work seamless and allow more effective communication.
Also published on the Atlassian Community.
Try Active Directory Attributes Sync
If you would like to know more about our app, take a free 30-day trial from the Atlassian Marketplace!